Phishing, spoofing, malware… do you really know the difference?
March 27, 2026 | Jordi Genescà Prat
Cibersecurity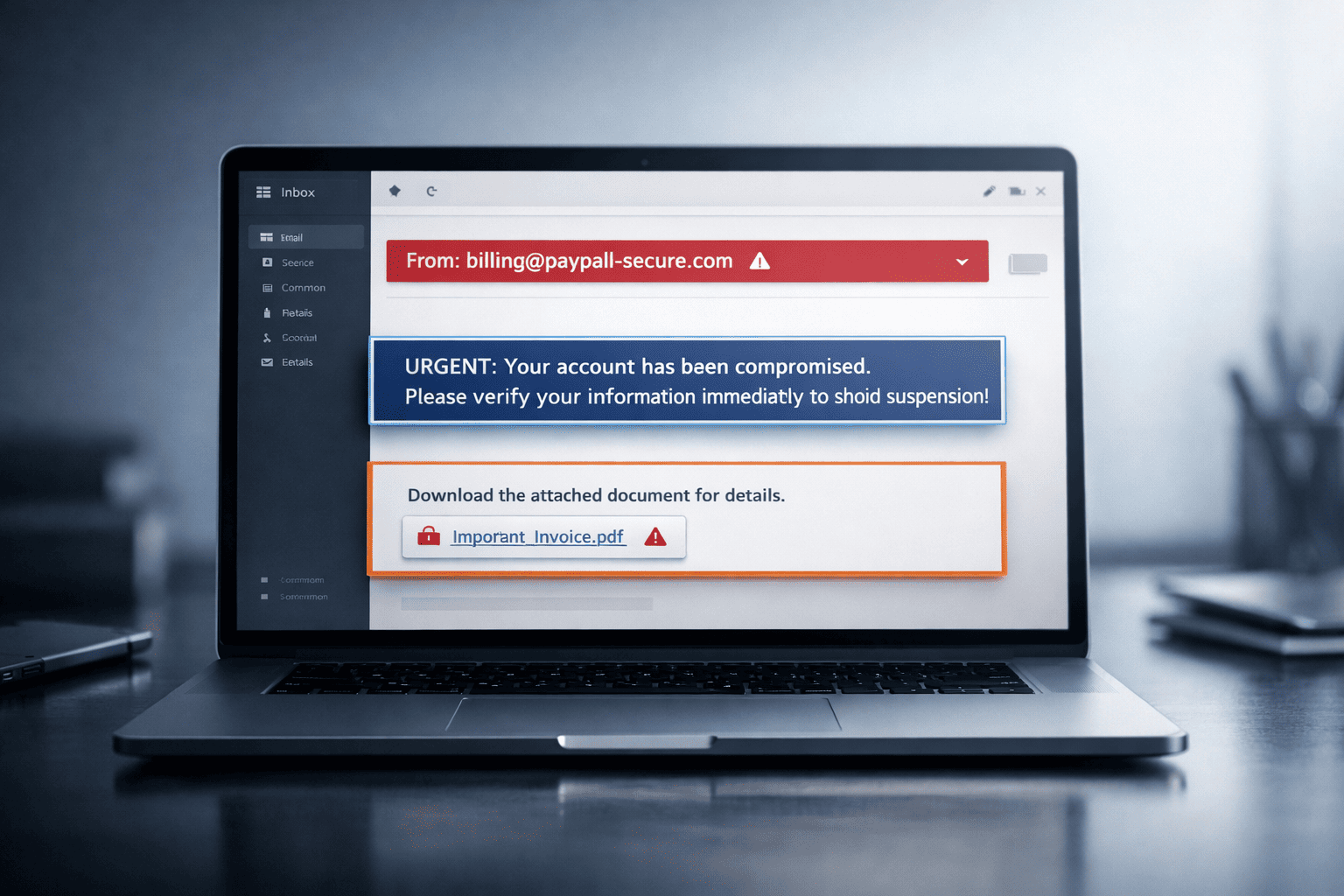
These are terms most people have heard, but very few can clearly distinguish. Phishing, spoofing and malware often appear together and are frequently used as if they meant exactly the same thing. But they don’t.
Understanding the difference is not just a technical detail. It’s a way to better understand how modern attacks actually work and what a company can do to reduce risk. Because when we talk about cybersecurity, not everything is simply “an attack”. There are different entry points, different objectives and different ways of deceiving users.
When everything seems the same… but isn’t
In everyday conversations, it’s common to hear phrases like “we’ve been targeted by phishing” when in reality something more complex has happened. That’s understandable, because many attacks combine multiple techniques at the same time.
A single attack may include:
- Identity impersonation in the sender (spoofing)
- A message designed to create urgency or trust (phishing)
- A malicious file or link (malware)
From the outside, it looks like a single threat. But in reality, these are different layers working together. And that combination is exactly what makes many attacks so effective.
Phishing: the art of deceiving the user
Phishing doesn’t primarily target technology. It targets people. It is a technique designed to trick users into doing something they shouldn’t: sharing credentials, clicking on a link or downloading a file. It doesn’t require complex vulnerabilities, just a message that feels legitimate.
Common examples include:
- Emails impersonating Microsoft, Google or known suppliers
- Urgent alerts from banks or financial services
- Internal-looking messages that appear to come from your own team
The goal is always the same: create trust to trigger action. And once that action happens, the attack has already started to succeed.
Spoofing: when identity can no longer be trusted
Spoofing shifts the focus. Here, the issue is not so much the content of the message, but its origin. The attacker makes an email, website or even a call appear to come from a legitimate source.
This can take forms such as:
- An email that appears to be sent from your own domain
- A supplier with a name almost identical to the real one
- A URL with a small change that goes unnoticed
When the origin appears trustworthy, suspicion disappears. And at that point, the rest of the attack becomes much more effective.
Spoofing is rarely the full attack on its own. It is what makes phishing far more convincing.
Malware: when the attack is already inside
Malware is the stage where the attack moves from possibility to reality within the system. It can arrive through an attachment, a download or even a seemingly legitimate website.
Once inside, the impact can vary widely:
- Theft of sensitive information
- Credential capture
- Remote access to systems
- Data encryption (ransomware)
In many cases, malware is not the starting point but the result. Someone has already been deceived, clicked where they shouldn’t or trusted something that looked safe.
How they combine in a real attack
To understand the difference more clearly, imagine a common scenario. An employee receives an email that appears to come from the IT department. The sender has been impersonated — this is spoofing.
The message claims there is a security issue and asks the user to update their password urgently — this is phishing.
The email includes a link to a page that closely mimics the corporate environment. The user trusts it, logs in and enters their credentials. From that moment on, the attacker has access to the account.
In other cases, the same link may trigger a download that installs malware on the device.
Everything happens within minutes. And it all starts with something that looks completely harmless.
Understanding the difference is what really protects your business
Many companies still believe these attacks are isolated incidents or only affect large organisations. The reality is very different. Attacks are increasingly automated, more frequent and harder to detect. They are not always targeting a specific company — they are looking for any vulnerability.
That’s why protection is not about preventing attacks entirely, but about reducing the chances of success. This means working across multiple layers: proper domain configuration (SPF, DKIM and DMARC), control over who can send emails on your behalf, detection of suspicious behaviour, basic user awareness and mechanisms to validate message authenticity.
When these measures are in place, attacks don’t disappear — but they become far less effective. And that difference is what truly matters.
If you want to learn more about how to protect your business against these types of threats and prevent impersonation, you can visit our page on phishing protection.
Because in cybersecurity, everything often starts with something small. And understanding that first step makes all the difference.